The U.K. and U.S. governments sanctioned 11 more individuals who were alleged members of the Russia-based TrickBot cybercrime gang.
The United States, in coordination with the United Kingdom, sanctioned eleven more individuals who are members of the Russia-based Trickbot cybercrime group. The sanctions were provided by the U.S. Department of the Treasury’s Office of Foreign Assets Control (OFAC).
Among the sanctioned individuals, there are administrators, managers, developers, and coders who have materially supported the operations of the Trickbot group.
“Today’s targets include key actors involved in management and procurement for the Trickbot group, which has ties to Russian intelligence services and has targeted the U.S. Government and U.S. companies, including hospitals.” reads the announcement made by the U.S. Department of the Treasury.
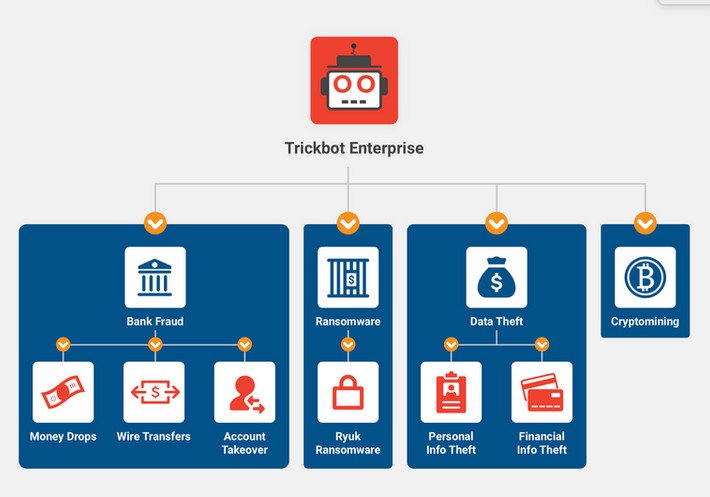
TrickBot is a popular Windows banking Trojan that has been around since October 2016, its authors have continuously upgraded it by implementing new features, including powerful password-stealing capabilities.
TrickBot initially partnered with Ryuk ransomware which used it for initial access in the network compromised by the botnet. Then Ryuk was replaced by Conti Ransomware gang who had been using Trickbot for the same purpose.
In 2021, the Conti gang used in exclusive the TrickBot to achieve initial access to the network of organizations worldwide.
Below is the list of sanctioned individuals:
This included targeting the U.S. Government and U.S. companies.
- Andrey Zhuykov was a central actor in the group and acted as a senior administrator. Andrey Zhuykov is also known by the online monikers Dif and Defender.
- Maksim Galochkin led a group of testers, with responsibilities for development, supervision, and implementation of tests. Maksim Galochkin is also known by the online monikers Bentley, Crypt, and Volhvb.
- Maksim Rudenskiy was a key member of the Trickbot group and the team lead for coders.
- Mikhail Tsarev was a manager with the group, overseeing human resources and finance. He was responsible for management and bookkeeping. Mikhail Tsarev is also known by the monikers Mango, Alexander Grachev, Super Misha, Ivanov Mixail, Misha Krutysha, and Nikita Andreevich Tsarev.
- Dmitry Putilin was associated with the purchase of Trickbot infrastructure. Dmitry Putilin is also known by the online monikers Grad and Staff.
- Maksim Khaliullin was an HR manager for the group. He was associated with the purchase of Trickbot infrastructure including procuring Virtual Private Servers. Maksim Khaliullin is also known by the online moniker Kagas.
- Sergey Loguntsov was a developer for the Trickbot group.
- Vadym Valiakhmetov worked as a coder for the Trickbot group and is known by the online monikers Weldon, Mentos, and Vasm.
- Artem Kurov worked as a coder with development duties in the Trickbot group. Artem Kurov is also known by the online moniker Naned.
- Mikhail Chernov was part of the internal utilities group for Trickbot and is also known by the online moniker Bullet.
- Alexander Mozhaev was part of the admin team responsible for general administrative duties and is also known by the online monikers Green and Rocco.
The investigation conducted by the UK National Crime Agency (NCA) revealed that the group extorted at least $180 million from victims globally, and at least £27 million from 149 UK victims. The ransomware operation also targeted UK hospitals, schools, local authorities and businesses.
“These cyber criminals thrive off anonymity, moving in the shadows of the internet to cause maximum damage and extort money from their victims.” UK Foreign Secretary James Cleverly said.
“Our sanctions show they cannot act with impunity. We know who they are and what they are doing.
By exposing their identities, we are disrupting their business models and making it harder for them to target our people, our businesses and our institutions.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Trickbot)
The post UK and US sanctioned 11 members of the Russia-based TrickBot gang appeared first on Security Affairs.