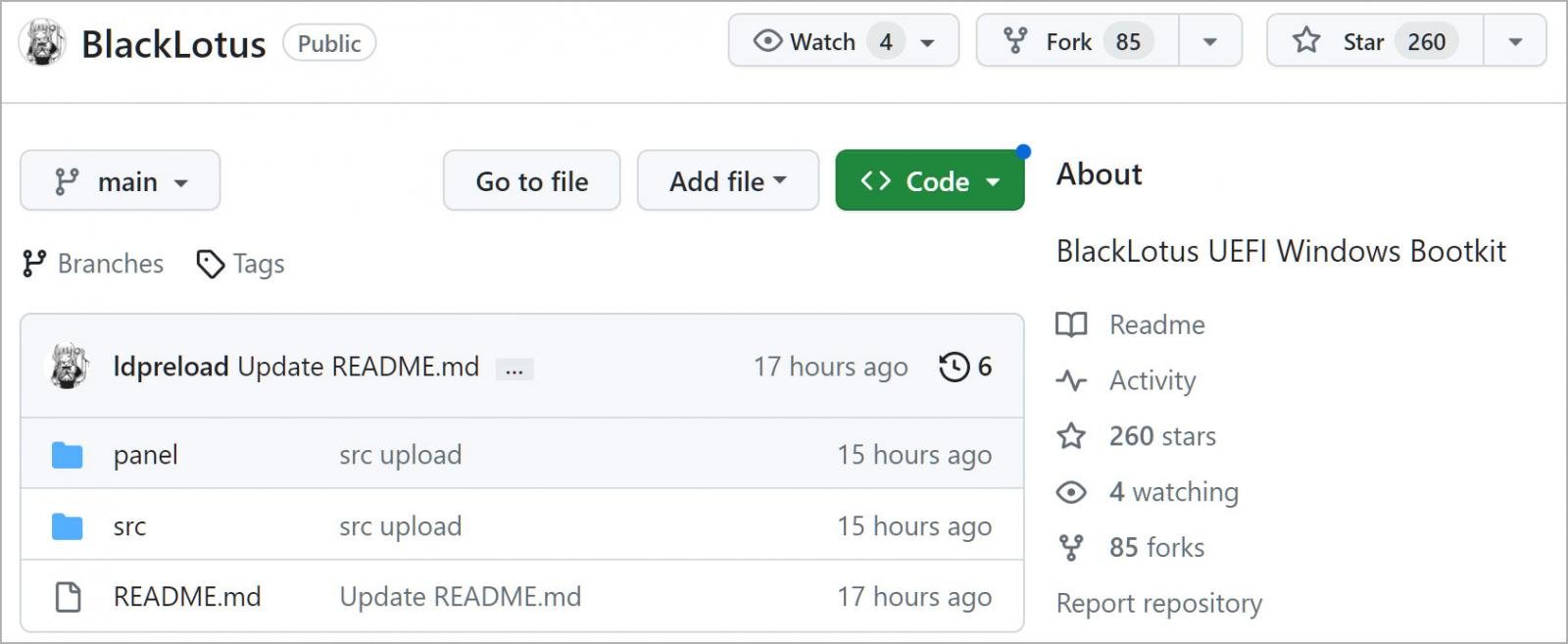
The source code for the BlackLotus UEFI bootkit has been published on GitHub and experts warn of the risks of proliferation of custom versions.
Researchers from ESET discovered in March a new stealthy Unified Extensible Firmware Interface (UEFI) bootkit, named BlackLotus, that is able to bypass Secure Boot on Windows 11.
Secure Boot is a security feature of the latest Unified Extensible Firmware Interface (UEFI) 2.3.1 designed to detect tampering with boot loaders, key operating system files, and unauthorized option ROMs by validating their digital signatures. “Detections are blocked from running before they can attack or infect the system specification.
BlackLotus is the first UEFI bootkit that is able to bypass the security feature on fully up-to-date Windows 11 systems.
The BlackLotus malware is a UEFI bootkit that is available for sale on hacking forums since at least October 2022. The powerful malware is offered for sale at $5,000, with $200 payments per new updates.
Black Lotus is written in assembly and C and is only 80kb in size, the malicious code can be configured to avoid infecting systems in countries in the CIS region.
The malware supports anti-virtualization, anti-debugging, and code obfuscation. Black Lotus is able to disable security solutions, including Hypervisor-protected Code Integrity (HVCI), BitLocker, and Windows Defender. The rootkit is able to bypass security defenses like UAC and Secure Boot, it is able to load unsigned drivers used to perform a broad range of malicious activities.
The threat is very stealthy, it can achieve persistence at the UEFI level with Ring 0 agent protection.
Black Lotus supports a full set of backdoor capabilities, it could be also used to potentially target IT and OT environments.
ESET researchers reported that the bootkit exploits the vulnerability CVE-2022-21894 to bypass UEFI Secure Boot and maintain persistence. This is the first publicly known bootkit that abuses this vulnerability in the wild.
“Exploiting CVE-2022-21894 to bypass the Secure Boot feature and install the bootkit. This allows arbitrary code execution in early boot phases, where the platform is still owned by firmware and UEFI Boot Services functions are still available.” reads the analysis published by the experts. “This allows attackers to do many things that they should not be able to do on a machine with UEFI Secure Boot enabled without having physical access to it, such as modifying Boot-services-only NVRAM variables. And this is what attackers take advantage of to set up persistence for the bootkit in the next step. “
The experts pointed out that despite the issue was addressed by Microsoft in January 2022, its exploitation is still possible as the affected, validly signed binaries have still not been added to the UEFI revocation list.

Upon successful installation of the bootkit, the malicious code deploys a kernel driver and an HTTP downloader, used for C2 communication, which can load additional user-mode or kernel-mode payloads.
The source code for the BlackLotus UEFI bootkit has been leaked on GitHub, this means that threat actors can use it to create their own variants, which include new exploits.
The public availability of the bootkit’s source code represents a significant risk mainly because it can be combined with new exploits and create new attack opportunities, according to
Alex Matrosov, CEO of the firmware security company Binarly, believes that the leaked source code doesn’t represent a significant threat because it isn’t complete
“However, the fact that it’s possible to combine them with new exploits like the BlackLotus campaign did was something unexpected to the industry and shows the real limitations of the current mitigations below the operating system.” explained Matrosov. “The BlackLotus leak shows how old rootkit and bootkit tricks, combined with new Secure Boot bypass vulnerabilities, can still be very effective in blinding a lot of modern endpoint security solutions.”
The researcher pointed out that BlackLotus was observed using the publicly known BatonDrop exploit.
Although the CVE-2022-21894 was patched in 2022, the impact was able to exploit the issue because the vulnerable binaries were still used as part of the UEFI.
“Enterprise defenders and CISOs need to understand that threats below the operating system are clear and present dangers to their environments. Since this attack vector has significant benefits for the attacker, it is only going to get more sophisticated and complex,” Matrosov concludes.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, BlackLotus)
The post The source code of the BlackLotus UEFI Bootkit was leaked on GitHub appeared first on Security Affairs.
 The leaked source code isn’t complete and contains mainly the rootkit part and bootkit code to bypass Secure Boot. Most of these tricks and techniques are previously known for years and don’t present significant impact.
The leaked source code isn’t complete and contains mainly the rootkit part and bootkit code to bypass Secure Boot. Most of these tricks and techniques are previously known for years and don’t present significant impact. our previous REsearch:
our previous REsearch: