A previously unknown ransomware group known as RA Group is targeting companies in U.S. and South Korea with leaked Babuk source code.
Cisco Talos researchers recently discovered a new ransomware operation called RA Group that has been active since at least April 22, 2023. The group has already compromised three organizations in the U.S. and one in South Korea.
The researchers assess with high confidence that the group is using the leaked Babuk ransomware source code.
A sample of the ransomware analyzed by Talos is written in C++ and was compiled on April 23, 2023. The binary has the debug path “C:\Users\attack\Desktop\Ransomware.Multi.Babuk.c\windows\x64\Release\e.pdb”. The researchers noticed that the path contains the same mutex name as the Babuk ransomware, a circumstance that suggests the malware borrows Babuk’s leaked source code.
Compromised organizations operate in different business verticals, including manufacturing, wealth management, insurance providers, and pharmaceuticals.
Like other ransomware operations, the RA Group also uses a double extortion model and runs a date leak site.
“This actor is expanding its operations at a fast pace. RA Group launched their data leak site on April 22, 2023, and on April 27, we observed the first batch of victims, three in total, followed by another one on April 28. We also observed the actor making cosmetic changes to their leak site after disclosing the victim’s details, confirming they are in the early stages of their operation.” reads the report published by Cisco Talos.
The RA Group is also attempting to sell the stolen data through its leak site.
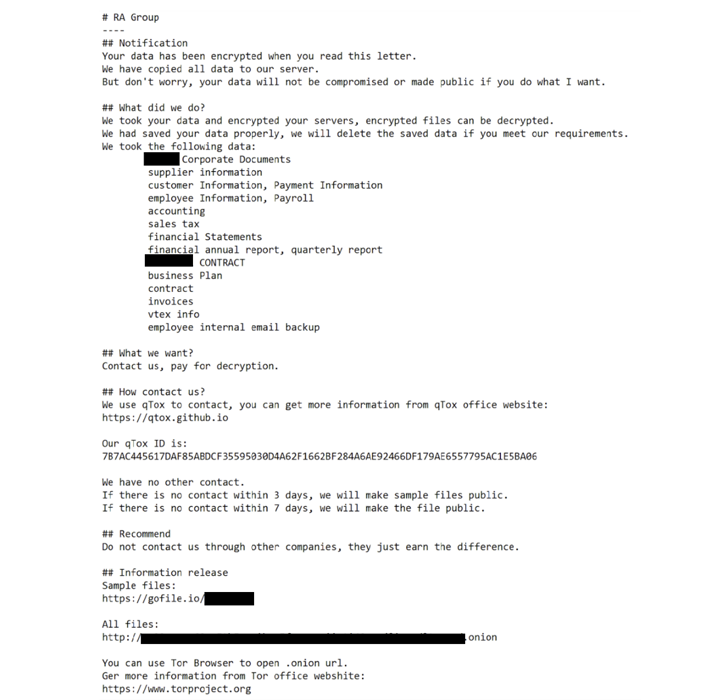
Once encrypted the victims files RA Group, the gang drops customized ransom notes (“How To Restore Your Files.txt.”), which include the victim’s name and a unique link to download the exfiltration proofs.
According to the ransom notes, in case the victim fails to contact the gang within three days, the group leaks the victim’s files.
The ransomware supports intermittent encryption to speed up the encryption process. Once encrypted the file, the malicious code deletes the contents of the victim machine’s Recycle Bin using the API SHEmptyRecyclebinA and deletes the volume shadow copy.
“RA Group’s ransomware executable uses the cryptography scheme with curve25519 and eSTREAM cipher hc-128 algorithm for encryption. This process encrypts only a certain part of the source file’s contents, not the entire file.” continues the report. “It uses WinAPI CryptGenRandom to generate cryptographically random bytes used as a private key for each victim.”
The ransomware appends the file extension “.GAGUP” to the name of the encrypted files.
The ransomware only targets files and folders that are not included in a hardcoded list, this trick allows to avoid encrypting files that can impair the infected system.
Cisco Talos provided Indicators of Compromise associated with the RA ransomware.
RA Group isn’t the only gang that uses the leaked Babuk source code, recently SentinelLabs researchers have identified 10 ransomware families using VMware ESXi lockers based on the source code of the Babuk ransomware that was leaked in 2021.
The experts pointed out that these ransomware families were detected through H2 2022 and H1 2023, a circumstance that suggests that an increasing number of threat actors is using the source code of the Babuk ransomware.
SentinelOne explained that the availability of the leaked source code allows threat actors to create ransomware to target Linux systems, even if they lack of expertise.
We are in the final!
Please vote for Security Affairs (https://securityaffairs.com/) as the best European Cybersecurity Blogger Awards 2022 – VOTE FOR YOUR WINNERS
Vote for me in the sections where is reported Securityaffairs or my name Pierluigi Paganini
Please nominate Security Affairs as your favorite blog.
Nominate Pierluigi Paganini and Security Affairs here here: https://docs.google.com/forms/d/e/1FAIpQLSepvnj8b7QzMdLh7vWEDQDqohjBUsHyn3x3xRdYGCetwVy2DA/viewform
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, cybercrime)
The post New RA Group ransomware gang is the latest group using leaked Babuk source code appeared first on Security Affairs.