Microsoft revealed that recent attacks against PaperCut servers aimed at distributing Cl0p and LockBit ransomware.
Microsoft linked the recent attacks against PaperCut servers to a financially motivated threat actor tracked as Lace Tempest (formerly DEV-0950). The group is known to be an affiliate of the Clop ransomware RaaS affiliate, it has been linked to GoAnywhere attacks and Raspberry Robin infection. Since April 13, Lace Tempest added the PaperCut exploits to its arsenal.
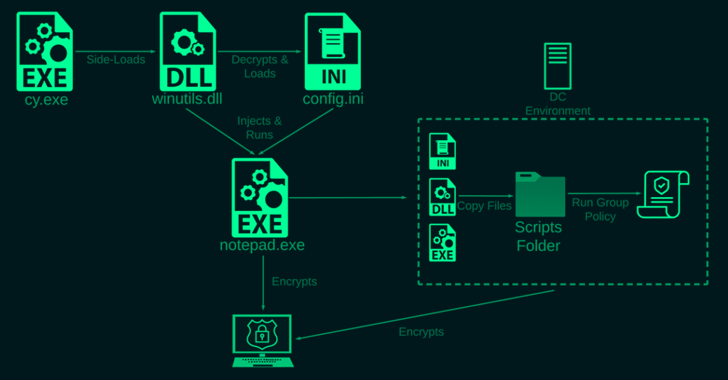
In the attack observed by Microsoft, the group ran multiple PowerShell commands to deliver a TrueBot DLL, which connected to a C2 server, attempted to steal LSASS credentials, and injected the TrueBot payload into the conhost.exe service.
Then Lace Tempest dropped a Cobalt Strike Beacon implant, gathered additional information on the target environment, and used WMI for lateral movement. The group used the file-sharing app MegaSync for data exfiltration.
Microsoft is also monitoring a separate cluster of attacks exploiting PaperCut flaws to deliver the Lockbit ransomware. The company warns that other financially motivated groups could adopt a similar infection chain.
About the author: Vilius Petkauskas, Senior Journalist at CyberNews
Blogger Awards 2022 – VOTE FOR YOUR WINNERS
Vote for me in the sections:
- The Teacher – Most Educational Blog
- The Entertainer – Most Entertaining Blog
- The Tech Whizz – Best Technical Blog
- Best Social Media Account to Follow (@securityaffairs)
Please nominate Security Affairs as your favorite blog.
Nominate here: https://docs.google.com/forms/d/e/1FAIpQLSfaFMkrMlrLhOBsRPKdv56Y4HgC88Bcji4V7OCxCm_OmyPoLw/viewform
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, PaperCut)
The post Crooks use PaperCut exploits to deliver Cl0p and LockBit ransomware appeared first on Security Affairs.