China-linked APT group GREF is behind a malware campaign distributing spyware via trojanized Signal and Telegram apps on Google Play
ESET researchers uncovered a cyberespionage campaign carried out by the China-linked APT group known as GREF that is distributing spyware via trojanized Signal and Telegram apps on Google Play and Samsung Galaxy stores.

The malware distributed by the nation-state actors is Android BadBazaar, which has been previously employed in attacks aimed at Uyghurs and other Turkic ethnic minorities.
The campaigns observed by the researchers are likely active since July 2020 and since July 2022, respectively.
The Android spyware was able to collect a broad range of information, including:
- Location (latitude and longitude)
- List of installed packages
- Call logs and geocoded location associated with the call
- Contacts information
- Installed Android apps
- SMS information
- Extensive device information, including the model, language, IMEI, IMSI, ICCID (SIM serial number), phone number, timezone, and centralized registry of the user’s online accounts
- Wi-Fi info (connected or not, and if connected, the IP, SSID, BSSID, MAC, netmask, gateway, DNS1, DNS2)
- Record phone calls
- Take pictures
- Data and database files from the trojanized app’s SharedPreferences directory
- Retrieve a list of files on the device that end in .ppt, .pptx, .docx, .xls, .xlsx, .doc, or .pdf
- Folders of interest as specified dynamically from the C2 server, including images from the camera and screenshots, Telegram, Whatsapp, GBWhatsapp, TalkBox, Zello attachments, logs, and chat history
Threat actors also used dedicated websites representing the malicious apps Signal Plus Messenger and FlyGram.
“Based on our telemetry, we were able to identify active Android campaigns where an attacker uploaded and distributed malicious apps that go by the names Signal Plus Messenger and FlyGram via the Google Play store, Samsung Galaxy Store, and dedicated websites, mimicking the Signal application (signalplus[.]org) and a Telegram alternative app (flygram[.]org).” reads the analysis published by ESET.
The rogue apps were designed to exfiltrate user data. FlyGram can be used to extract basic device information, and sensitive data, such as contact lists, call logs, and the list of Google Accounts. The app can also exfiltrate some information and settings related to Telegram except the contact list, messages, or any other sensitive information.
“Both apps were created by the same developer, share the same malicious features, and the app descriptions on both stores refer to the same developer website, signalplus[.]org. The domain was registered on February 15th, 2022, and provides a link to download the malicious Signal Plus Messenger application either from Google Play or directly from the website” continues the report.
Signal Plus Messenger can collect device data and sensitive information, and spy on the victim’s Signal communications.
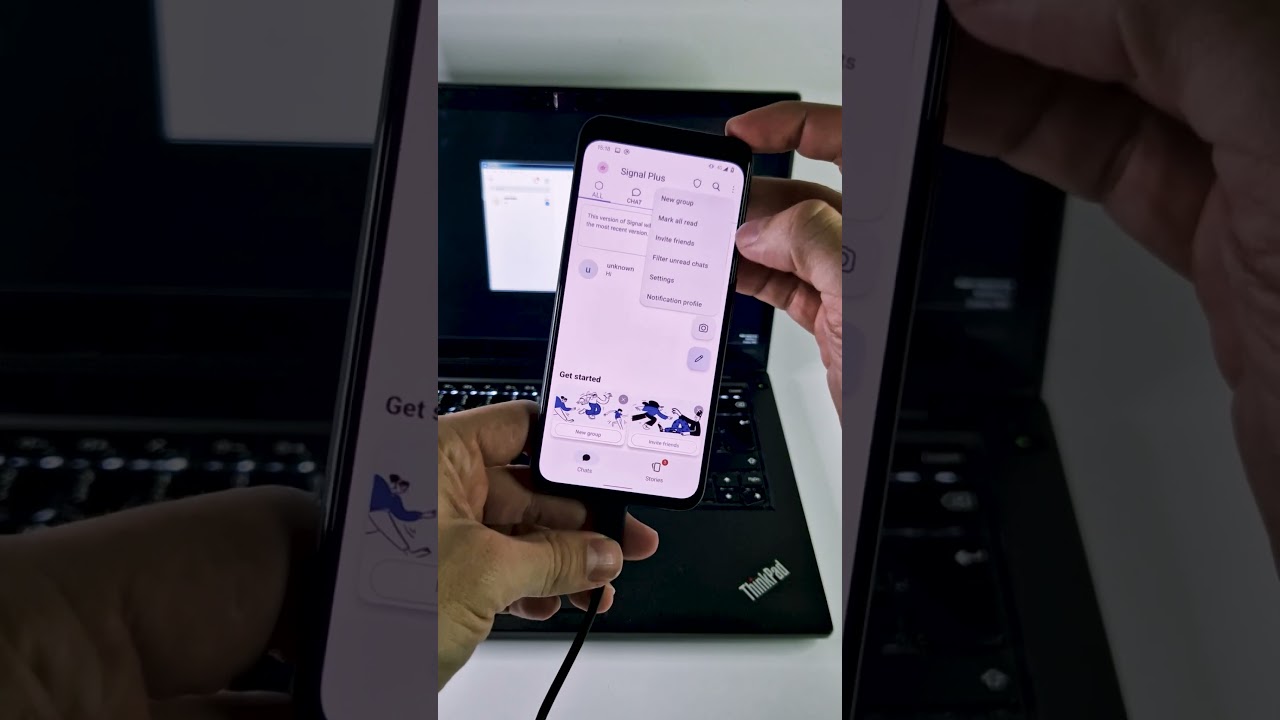
The following video shows how the attacker associates the compromised device to the attacker’s Signal account without any user interaction.
ESET reported Signal Plus Messenger to both Google Play and Samsung Galaxy Store on April 27, 2023. Google removed the tainted app on May 23rd, 2023. Google removed FlyGram from Google Play after January 6, 2021. The researchers noticed that at the time of writing, both apps are still available on the Samsung Galaxy Store.
ESET observed infections in Ukraine, Poland, the Netherlands, Spain, Portugal, Germany, Hong Kong, and the United States.
The report includes indicators of compromise (IoCs) for these threats.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Signal)
The post Chinese GREF APT distributes spyware via trojanized Signal and Telegram apps on Google Play and Samsung Galaxy stores appeared first on Security Affairs.