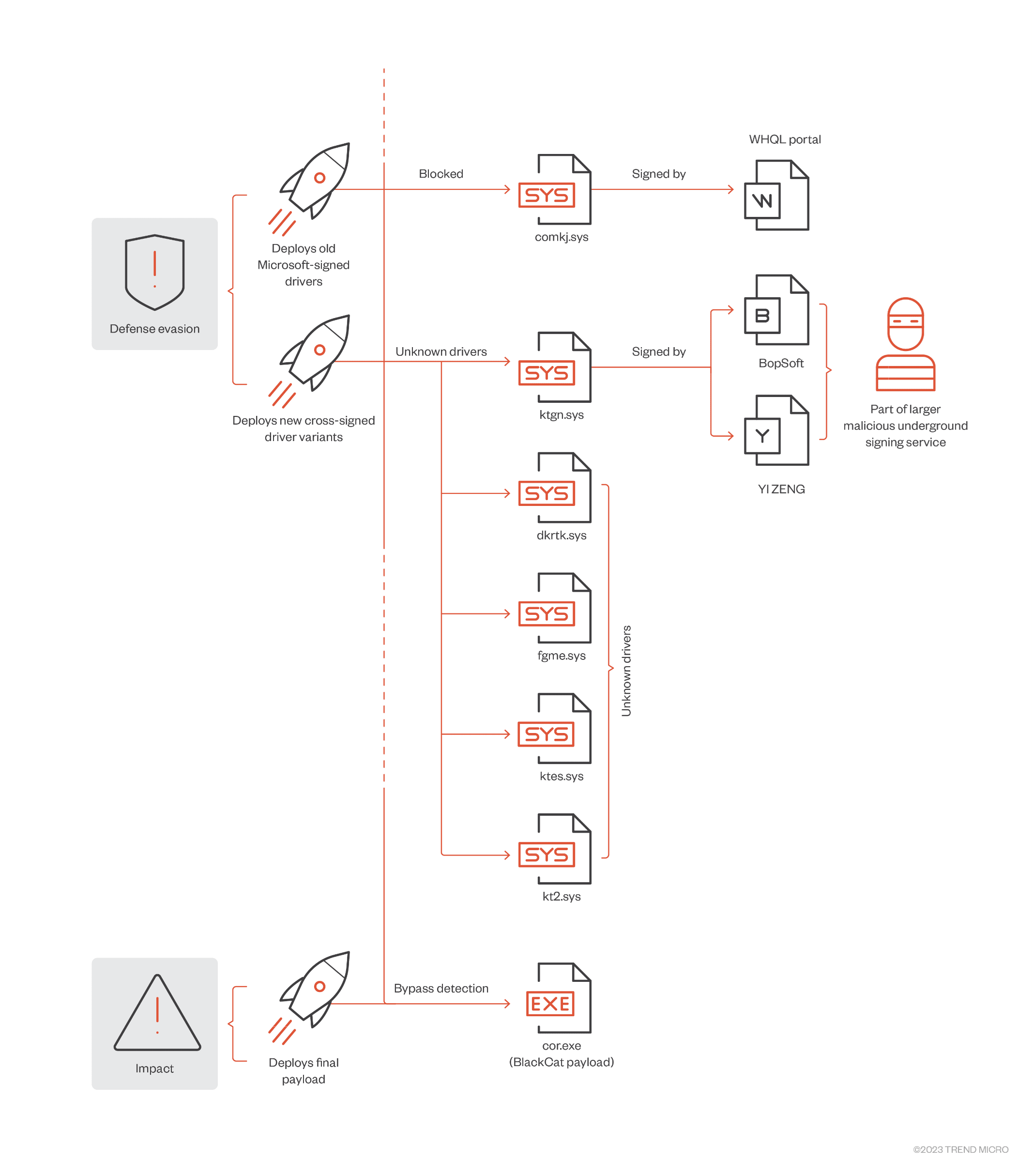
Experts spotted the ALPHV/BlackCat ransomware group using signed malicious Windows kernel drivers to evade detection.
Trend Micro researchers shared details about ALPHV/BlackCat ransomware incident that took place on February 2023. A BlackCat affiliate employed signed malicious Windows kernel drivers to evade detection.
Experts believe the driver is a new version of the malware reported in December 2022 by Mandiant, Sophos and Sentinel One, via a coordinated disclosure.
The attackers attempted to deploy the driver (ktgn.sys) previously analyzed by Mandiant, which is signed through Microsoft signing portals.
The use of a Windows kernel driver, which runs with the highest privileges in the OS, allows attackers to kill any process associated with defense products.
The researchers pointed out that even if the certificate that was used to sign the ktgn.sys driver has been revoked, the driver will still load on 64-bit Windows systems with enforced signing policies.
The kernel driver employed in the attack exposes an IOCTL interface that allows the user Agent tjr.exe to issue commands that the driver will execute with kernel privileges.
“The User Agent tjr.exe, which is protected via a virtual machine, drops the kernel driver to the user temporary directory C:\%User%\AppData\Local\Temp\Ktgn.sys. It then installs the dropped driver with the name ktgn and the start value = System (to start when the system restarts).” reads the analysis from Trend Micro. “From our analysis of what occurs when a user interfaces with this driver, we observed that it only uses one of the exposed Device Input and Output Control (IOCTL) code — Kill Process, which is used to kill security agent processes installed on the system.”
This client supports ten different commands that can be sent to the kernel driver through the IOCTL interface:
| IOCTL Code | Description |
|---|---|
| 222088h | Activate Driver |
| 22208Ch | Deactivate Driver |
| 222094h | Kill Process |
| 222184h | Delete File |
| 222188h | Force Delete File |
| 22218Ch | Copy File |
| 222190h | Force Copy File |
| 2221C8h | Register Process/Thread Object notification |
| 2221C4h | Unregister Process/Thread Object notification |
| 222264h | Reboot the system |
The driver is obfuscated using Safengine Protector v2.4.0.0 tool to prevent static analysis.
The use of an updated version of the driver also demonstrates a link between the ransomware gang and the UNC3944/Scattered Spider groups that was spotted using a predecessor of the driver by Mandiant.
The experts noticed that the driver is still under development and testing since it is not structured well and some of its functions currently are not working.
“Malicious actors that are actively seeking high-privilege access to the Windows operating system use techniques that attempt to combat the increased protection on users and processes via endpoint protection platform (EPP) and endpoint detection and response (EDR) technologies. Because of these added layers of protection, attackers tend to opt for the path of least resistance to get their malicious code running via the kernel layer (or even lower levels). This is why we believe that such threats will not disappear from threat actors’ toolkits anytime soon.” concludes the report. “Malicious actors will continue to use rootkits to hide malicious code from security tools, impair defenses, and fly under the radar for long periods.”
We are in the final!
Please vote for Security Affairs (https://securityaffairs.com/) as the best European Cybersecurity Blogger Awards 2022 – VOTE FOR YOUR WINNERS
Vote for me in the sections where is reported Securityaffairs or my name Pierluigi Paganini
Please nominate Security Affairs as your favorite blog.
Nominate Pierluigi Paganini and Security Affairs here here: https://docs.google.com/forms/d/e/1FAIpQLSepvnj8b7QzMdLh7vWEDQDqohjBUsHyn3x3xRdYGCetwVy2DA/viewform
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Blackcat ransomware)
The post BlackCat Ransomware affiliate uses signed kernel driver to evade detection appeared first on Security Affairs.