Skip to content
Ubuntu security team noted after extensive testing that DLA-3495-1 was incomplete as one PoC for CVE-2022-2400 (particularly the chroot escape) was still working on the patched version of the package.…
Daniel Moghimi discovered Gather Data Sampling (GDS), a hardware vulnerability for Intel CPUs which allows unprivileged speculative access to data which was previously stored in vector registers.…
Multiple security issues have been found in the Mozilla Firefox web browser, which could potentially result in the execution of arbitrary code, bypass of the same-origin policy, spoofing or sandbox bypass.…
Multiple security vulnerabilities were discovered in HDF5, a Hierarchical Data Format and a library for scientific data. Memory leaks, out-of-bound reads and division by zero errors may lead to a denial of service when processing a malformed HDF file.…
Multiple security issues were discovered in Thunderbird, which could result in denial of service or the execution of arbitrary code. For Debian 10 buster, these problems have been fixed in version…
A security vulnerability has been discovered in libhtmlcleaner-java, a Java HTML parser library. An attacker was able to cause a denial of service (StackOverflowError) if the parser runs on user supplied input with deeply nested HTML elements. This update introduces…
Multiple security vulnerabilities have been discovered in OpenImageIO, a library for reading and writing images. Buffer overflows and out-of-bounds read and write programming errors may lead to a denial of service (application crash) or the execution of arbitrary code if…
A stack overflow in the MD5 function has been fixed in pdfcrack, a tool for recovering passwords and content from PDF files. For Debian 10 buster, this problem has been fixed in version 0.16-3+deb10u1.…
Multiple vulnerabilities have been found in the version of yajl bundled with burp, a simple cross-platform network BackUp and Restore Program. yajl is a JSON parser and small validating JSON generator.…
An incorrect Authentication Tag length usage was discovered in cjose, a C library implementing the Javascript Object Signing and Encryption (JOSE) standard, which could lead to integrity compromise.…
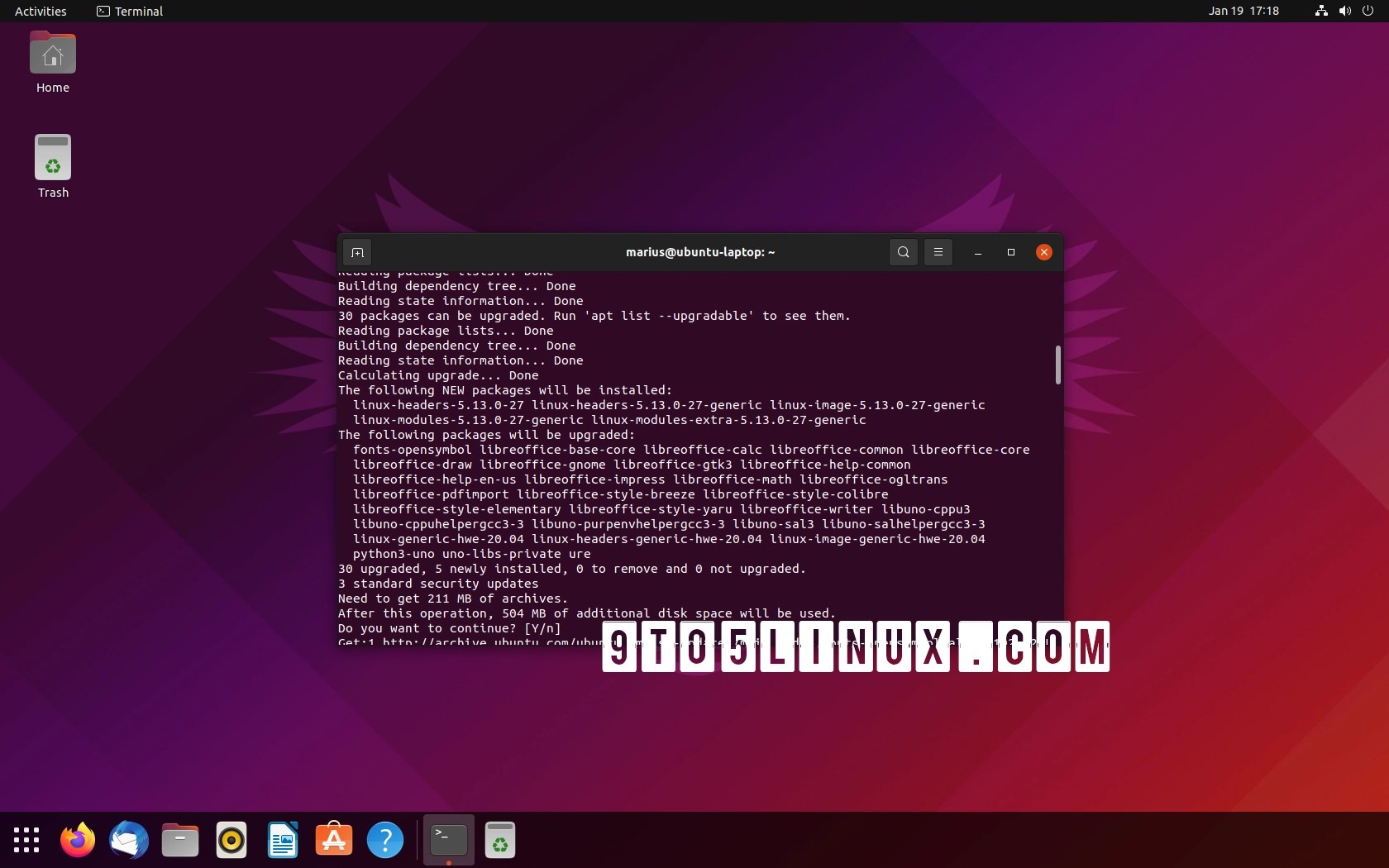
Several vulnerabilities have been discovered in the Linux kernel that may lead to a privilege escalation, denial of service or information leaks.…
It was discovered that there was a protential LDAP injection vulnerability in Bouncy Castle, a cryptographic library for Java. During the certificate validation process, bouncycastle used the certificate's "Subject Name" into an LDAP search filter without any…
Multiple vulnerabilities were found in tiff, a library and tools providing support for the Tag Image File Format (TIFF).…
Tavis Ormandy discovered that under specific microarchitectural circumstances, a vector register in "Zen 2" CPUs may not be written to 0 correctly. This flaw allows an attacker to leak register contents across concurrent processes, hyper threads and virtualized guests.…
A security issue was discovered in Thunderbird, which could result in spoofing of filenames of email attachments. For Debian 10 buster, this problem has been fixed in version…
It was discovered that the domain check in libmail-dkim-perl, a Perl module to cryptographically identify the sender of email, compares i and d tags case sensitive when t=s is set on the DKIM key which causes spurious fails of legitimate…
Several vulnerabilities have been discovered in the Linux kernel that may lead to a privilege escalation, denial of service or information leaks.…
Arbitrary file write vulnerabilities were discovered in pandoc, an Haskell library and CLI tool for converting from one markup format to another. These vulnerabilities can be triggered by providing a specially crafted image element in the input when generating files…
A memory allocation issue was found in iperf3, the Internet Protocol bandwidth measuring tool, that may cause a denial of service when encountering a certain invalid length value in TCP packets.…
Multiple multiple vulnerabilities were discovered in plugins for the GStreamer media framework and its codecs and demuxers, which may result in denial of service or potentially the execution of arbitrary code if a…
文 » A
Scroll Up
×
![]()